2020. 3. 22. 18:32ㆍ카테고리 없음
. Written in, 1.0 and 4-clause Website OpenSSL is a software library for applications that secure communications over against eavesdropping or need to identify the party at the other end. It is widely used in Internet web servers, serving a majority of all web sites. OpenSSL contains an implementation of the protocols. The core, written in the, implements basic functions and provides various utility functions. Wrappers allowing the use of the OpenSSL library in a variety of computer languages are available.
Versions are available for most and operating systems (including, and the various open-source operating systems),. Contents. Project history The OpenSSL project was founded in 1998 to provide a free set of encryption tools for the code used on the Internet. It is based on a fork of by Eric Andrew Young and Tim Hudson, which unofficially ended development on December 17, 1998, when Young and Hudson both went to work for. The initial founding members were Mark Cox, Ralf Engelschall, Stephen Henson, and Paul Sutton.
The OpenSSL management committee currently consists of 7 people. There are 13 developers with commit access (many of whom are also part of the OpenSSL management committee).
There are only two full-time employees (fellows) and the remainder are volunteers. The project has a budget of less than one million USD per year and relies primarily on donations. Development of TLS 1.3 is sponsored by Akamai. Algorithms OpenSSL supports a number of different cryptographic algorithms:, ( is supported using since version 1.0. ) FIPS 140-2 compliance As of December 2012, OpenSSL is one of two programs involved in validation under the computer security standard by the 's (NIST) (CMVP).

(OpenSSL itself is not validated, but a component called the OpenSSL FIPS Object Module, based on OpenSSL, was created to provide many of the same capabilities). A certificate was first awarded in January 2006 but revoked in July 2006 'when questions were raised about the validated module’s interaction with outside software.' The certification was reinstated in February 2007. Licensing OpenSSL is double licensed under the OpenSSL License and the SSLeay License, which means that the terms of both licenses apply. The OpenSSL License is 1.0 and SSLeay License bears some similarity to a 4-clause. As the OpenSSL License is 1.0, but not Apache License 2.0, it requires the phrase 'this product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit' to appear in advertising material and any redistributions (Sections 3 and 6 of the OpenSSL License).
Due to this restriction, the OpenSSL License and the Apache License 1.0 are incompatible with the. Some GPL developers have added an OpenSSL exception to their licenses that specifically permits using OpenSSL with their system. GNU and both use such exceptions. Some packages (like ) explicitly modify the GPL license by adding an extra section at the beginning of the license documenting the exception. Other packages use the -licensed and -licensed, which both perform the same task. OpenSSL announced in August 2015 that it would require most contributors to sign a (CLA), and that OpenSSL would eventually be under the terms of. This process commenced in March 2017.
Notable vulnerabilities Timing attacks on RSA Keys On March 14, 2003, a timing attack on RSA keys was discovered, indicating a vulnerability within OpenSSL versions 0.9.7a and 0.9.6. This vulnerability was assigned the identifier CAN-2003-0147 by the (CVE) project. Was not turned on by default by OpenSSL, since it is not easily possible to when providing SSL or TLS using OpenSSL.
Almost all SSL enabled Apaches were affected, along with many other applications of OpenSSL. Timing differences on the number of extra reductions along and use of Karatsuba and normal integer multiplication algorithms meant that it was possible for local and remote attackers to obtain the private key of the server. Denial of Service ASN.1 parsing OpenSSL 0.9.6k had a bug where certain sequences triggered a large number of recursions on Windows machines, discovered on November 4, 2003. Windows could not handle large recursions correctly, so OpenSSL would crash as a result.
Being able to send arbitrary large numbers of ASN.1 sequences would cause OpenSSL to crash as a result. A to a SSL/TLS enabled server could accept ASN.1 sequences and crash. OCSP stapling vulnerability When creating a handshake, the client could send an incorrectly formatted ClientHello message, leading to OpenSSL parsing more than the end of the message. Assigned the identifier CVE-2011-0014 by the CVE project, this affected all OpenSSL versions 0.9.8h to 0.9.8q and OpenSSL 1.0.0 to 1.0.0c. Since the parsing could lead to a read on an incorrect memory address, it was possible for the attacker to cause a DOS. It was also possible that some applications expose the contents of parsed extensions, leading to an attacker being able to read the contents of memory that came after the ClientHello. ASN.1 BIO vulnerability When using Basic Input/Output (BIO) or FILE based functions to read untrusted format data, OpenSSL is vulnerable.
This vulnerability was discovered on April 19, 2012, and was assigned the CVE identifier CVE-2012-2110. While not directly affecting the SSL/TLS code of OpenSSL, any application that was using ASN.1 functions (particularly d2iX509 and d2iPKCS12) were also not affected. SSL, TLS and DTLS Plaintext Recovery Attack In handling CBC cipher-suites in SSL, TLS, and DTLS, OpenSSL was found vulnerable to a timing attack during the MAC processing. Nadhem Alfardan and Kenny Paterson discovered the problem, and published their findings on February 5, 2013. The vulnerability was assigned the CVE identifier CVE-2013-0169. The vulnerability affected all OpenSSL versions, and was only partially mitigated by using the OpenSSL FIPS Object Module and enabling FIPS mode. Predictable private keys (Debian-specific) OpenSSL's pseudo- acquires entropy using complex programming methods, described as poor coding practice.
To keep the analysis tool from issuing associated warnings, a maintainer of the distribution applied a to the Debian's variant of the OpenSSL suite, which inadvertently broke its random number generator by limiting the overall number of private keys it could generate to 32,768. The broken version was included in the Debian release of September 17, 2006 (version 0.9.8c-1), also compromising other Debian-based distributions, for example. Any key generated with the broken random number generator was compromised, as well as the data encrypted with such keys; moreover, ready-to-use are easily available. The error was reported by Debian on May 13, 2008.
On the Debian 4.0 distribution (etch), these problems were fixed in version 0.9.8c-4etch3, while fixes for the Debian 5.0 distribution (lenny) were provided in version 0.9.8g-9. Heartbleed. A logo representing the Heartbleed bug OpenSSL versions 1.0.1 through 1.0.1f had a severe memory handling in their implementation of the Heartbeat Extension that could be used to reveal up to 64 of the application's memory with every (CVE-2014-0160). By reading the memory of the web server, attackers could access sensitive data, including the server's. This could allow attackers to decode earlier communications if the encryption protocol used does not ensure. Knowledge of the private key could also allow an attacker to mount a against any future communications.
The vulnerability might also reveal unencrypted parts of other users' sensitive requests and responses, including and passwords, which might allow attackers to of another user of the service. At its disclosure on April 7, 2014, around 17% or half a million of the Internet's secure certified by were believed to have been vulnerable to the attack. However, Heartbleed can affect both the server and client. CCS Injection Vulnerability CCS Injection Vulnerability (CVE-2014-0224) is a security bypass vulnerability that exists in OpenSSL.
The vulnerability is due to a weakness in OpenSSL methods used for keying material. This vulnerability can be exploited through the use of a man-in-the-middle attack, where an attacker may be able to decrypt and modify traffic in transit. A remote unauthenticated attacker could exploit this vulnerability by using a specially crafted handshake to force the use of weak keying material. Successful exploitation could lead to a security bypass condition where an attacker could gain access to potentially sensitive information. The attack can only be performed between a vulnerable client and server. OpenSSL clients are vulnerable in all versions of OpenSSL before the versions 0.9.8za, 1.0.0m and 1.0.1h. Servers are only known to be vulnerable in OpenSSL 1.0.1 and 1.0.2-beta1.
Users of OpenSSL servers earlier than 1.0.1 are advised to upgrade as a precaution. ClientHello sigalgs DoS This vulnerability (CVE-2015-0291) allows anyone to take a certificate, read its contents and modify it accurately to abuse the vulnerability causing a certificate to crash a client or server. If a client connects to an OpenSSL 1.0.2 server and renegotiates with an invalid signature algorithms extension, a null-pointer dereference occurs. This can cause a DoS attack against the server. A Stanford Security researcher, David Ramos, had a private exploit and presented it before the OpenSSL team where they patched the issue.
OpenSSL classified the bug as a high-severity issue, noting version 1.0.2 was found vulnerable. Key Recovery Attack on Diffie Hellman small subgroups This vulnerability (CVE-2016-0701) allows, when some particular circumstances are met, to recover the OpenSSL server's private Diffie–Hellman key. An Adobe System Security researcher, Antonio Sanso, privately reported the vulnerability.
OpenSSL classified the bug as a high-severity issue, noting only version 1.0.2 was found vulnerable. Forks Agglomerated SSL In 2009, after frustrations with the original OpenSSL API, Marco Peereboom, an OpenBSD developer at the time, forked the original API by creating Agglomerated SSL (assl), which reuses OpenSSL API under the hood, but provides a much simpler external interface. It has since been deprecated in light of the fork circa 2016. LibreSSL. Retrieved 2018-11-20. Laurie, Ben (1999-01-06). Ssl-users (Mailing list).
Retrieved 2018-10-29. OpenSSL Software Foundation. Retrieved 2018-07-22. OpenSSL Software Foundation.
Retrieved 2018-07-22. Marquess, Steve (2017-01-19). Openssl-announce (Mailing list).
Retrieved 2018-11-09. OpenSSL Software Foundation. Retrieved 2016-09-26. OpenSSL Software Foundation. Retrieved 2016-09-26. Archived from on 2015-01-20.
Retrieved 2017-02-20. Retrieved 2017-02-20. Retrieved 2017-02-20.
^ Caswell, Matt (2018-09-11). OpenSSL Foundation. Inc., OpenSSL Foundation.
Caswell, Matt (2018-02-08). OpenSSL Foundation. Caswell, Matt (2018-09-11). OpenSSL Foundation. Archived from on 2013-04-15. Retrieved 2017-08-29. Retrieved 2012-11-05.
Retrieved 2012-12-19. Archived from on 2007-10-10. Archived from on 2008-01-02. Archived from on 12 February 2011.
Retrieved 30 November 2010. Retrieved 24 January 2013. Salz, Rich (1 August 2015). Retrieved 23 August 2015. Archived from on 2018-07-18. Retrieved 2018-08-06. Retrieved 25 Aug 2014.
Mac Openssl Devel
Retrieved 2015-08-12. Retrieved 2015-06-19.
Retrieved 2015-08-12. May 13, 2008.
OpenSSL.org (7 April 2014). Retrieved 9 April 2014. OpenSSL (2014-04-07). Retrieved 2014-04-08. Codenomicon Ltd (2014-04-08). Retrieved 2014-04-08.
Retrieved 25 Aug 2014. Mutton, Paul (8 April 2014).
Netcraft Ltd. Retrieved 8 April 2014. Cyberoam Threat Research Labs. Brandon Stosh. Retrieved 2015-02-10. OpenBSD journal.
21 April 2014. Retrieved 21 April 2014. BoringSSL. Ars Technica.
Adam Langley's Weblog. 24 June 2014. External links Wikimedia Commons has media related to.
Openssl Alternatives For Mac Os
by Mark McLoughlin.
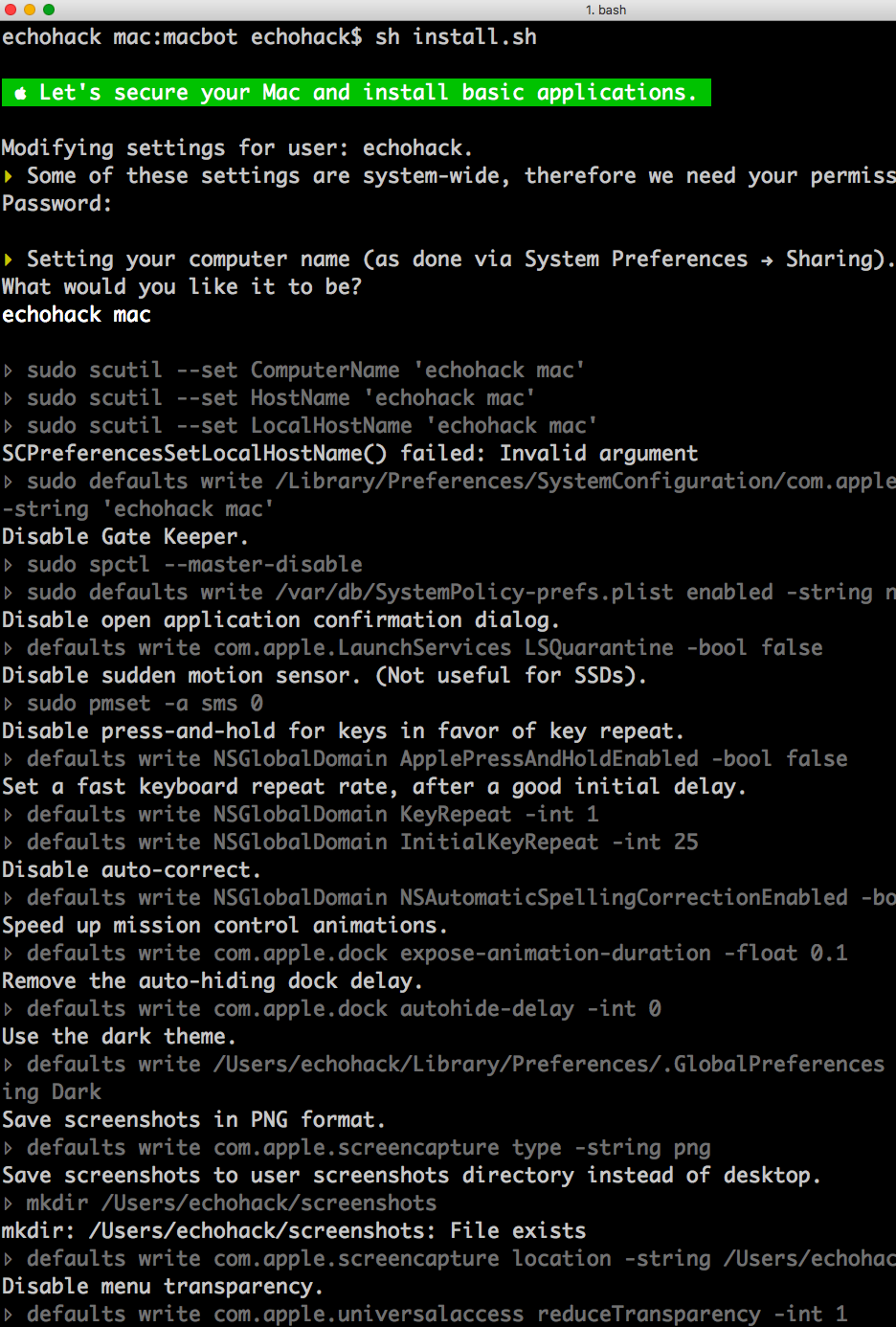
Based on from DarkLighting, here's the command I came up with using nested subshells. Openssl req -new -sha256 -key domain.key -subj '/C=US/ST=CA/O=Acme, Inc./CN=example.com' -reqexts SAN -config. This is my solution to finally generate a working self signed cert, based on the answers above(The accepted answer don't work for me): openssl genrsa -out ca.key 2048 openssl req -new -x509 -days 365 -key ca.key -subj '/C=CN/ST=GD/L=SZ/O=Acme, Inc./CN=Acme Root CA' -out ca.crt openssl req -newkey rsa:2048 -nodes -keyout server.key -subj '/C=CN/ST=GD/L=SZ/O=Acme, Inc./CN=.example.com' -out server.csr openssl x509 -req -extfile.
As of OpenSSL 1.1.1, providing subjectAltName directly on command line becomes much easier, with the introduction of the -addext flag to openssl req (via ). The commit an example to the: Example of giving the most common attributes (subject and extensions) on the command line: openssl req -new -subj '/C=GB/CN=foo' -addext 'subjectAltName = DNS:foo.co.uk' -addext 'certificatePolicies = 1.2.3.4' -newkey rsa:2048 -keyout key.pem -out req.pem This has been merged into the master branch of the, and as of April 18 2018 can be installed via a git pull + compile (or via Homebrew if on OS X: brew install -devel openssl@1.1). Note that if you have set the config attribute 'reqextensions' at section 'req' in openssl.cfg, it will ignore the command-line parameter. The following command demonstrates how to generate a self-signed certificate with SAN for example.com and example.net. It is portable in the sense that we don't have to mess around with (or even know about) the location of the openssl.cnf file: openssl req -x509 -newkey rsa:4096 -sha256 -days 3650 -nodes -keyout example.key -out example.crt -subj '/CN=example.com' -extensions san -config.